“What can I use a smart card for?”
One of the most common uses of smart cards in the United States is in banking, you are likely using a smart card, every time you use a debit or credit card. Smart chip cards are the most secure cards that hold data, requiring the card to make direct contact with the card reader for data to be transmitted, unlike RFID which can transmit within close proximity. The data can only be read by the chip operating system. Because of this, smart cards are typically used in environments requiring high security like; computer security systems, healthcare, electronic cash, wireless communications, mass transit, government identification, and banking.
Aside from the smart cards we all know and love…our credit cards, smart cards are used in a variety of settings. In healthcare they are used for easy and secure transference of patient data allowing for instant access and updating when necessary. In wireless communications we know smart cards as SIM cards (Subscriber Identity Molecules), this is what makes our phone unique to us and manages our mobile plan, so we can be billed properly. Many computer operating systems have started programming for the use of smart cards as a replacement for usernames and passwords. If you aren’t already, soon you’ll be putting a chip card into your computer and that chip will tell the network what privileges you have.
As data security threats increase smart cards will become more and more common. Here is what you need to know about how they work.
How Smart Card Chips Work:
Smart cards are generally made of plastic and embedded with an integrated circuit chip (ICC). The inside contains a microprocessor, random access memory (RAM), and data storage under a gold contact pad. That little chip is like a mini computer with an operating system and can have a file structure with secret keys and encryption for full security. The chip is also interactive, meaning it can receive input, deliver, and store 2,000-8,000 of bytes of data.
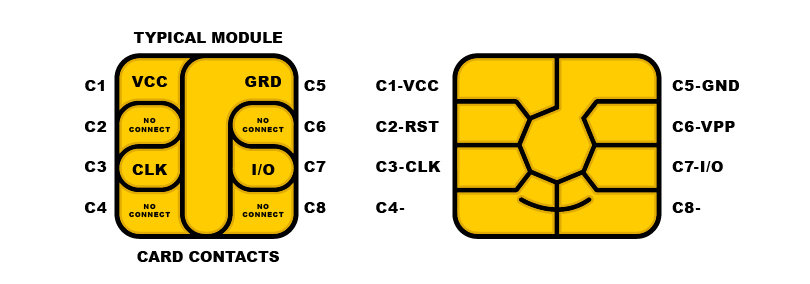
If you were to take all the chip cards out of your wallet and compare them, you will see that there are slight variations in chips. Below is an example of a chip’s different contacts and what their purpose is.
As stated above, the chip can only be accessed by the chip operating system. So, reading the chip requires card readers that are specifically pinned to the card. ISO 7816 is the standard that describes smart card chips and the interface.
When the chip card is inserted into the card reader they communicate with one another, if they are speaking the same language (if their messages match) they can work together to transfer information to the mainframe the reader is connected to or back to the card itself. This can be as simple as granting access to a door in a building or reading and writing data to the card.
Example Time:
It is a busy day at the University for Alyssa. She uses her University ID (that is a smart chip card) to check out several library books for a research paper. Then she uses her ID in the cafeteria debit her meal plan for lunch. After lunch she heads to the University Book Store where she uses her ID to pay for new University sweatshirt. Then she heads her dorm room to study where she needs to scan her ID to get in the door.
“How do I encode a smart chip card?”
This is not an easy question to answer in a blog post and taking this step will require someone with knowledge of your Company’s chip operating system. Depending on the type of smart chip card you have, different groups of data can be stored and programmed to different things, like the example above. Fields and parameters need to be set up in the chip operating system for each group of data you want on the card.
Once you have all that information, you can use ID creation software programs and ID card printers to help you program individual cards. ID Maker 3.0 is capable of programming MIFARE Classic and several types of iClass cards. To do so, you need to be well versed in the data you are programming to the card, ensuring the right bits of data are put into the right bins or the card won’t work.